Our Latest Blogs
- What Is Threat Hunting? How Proactive Security Prevents BreachesQuick Summary Threat hunting is the proactive, analyst-led search for threats that have already bypassed automated defences and are hiding… Read more: What Is Threat Hunting? How Proactive Security Prevents Breaches
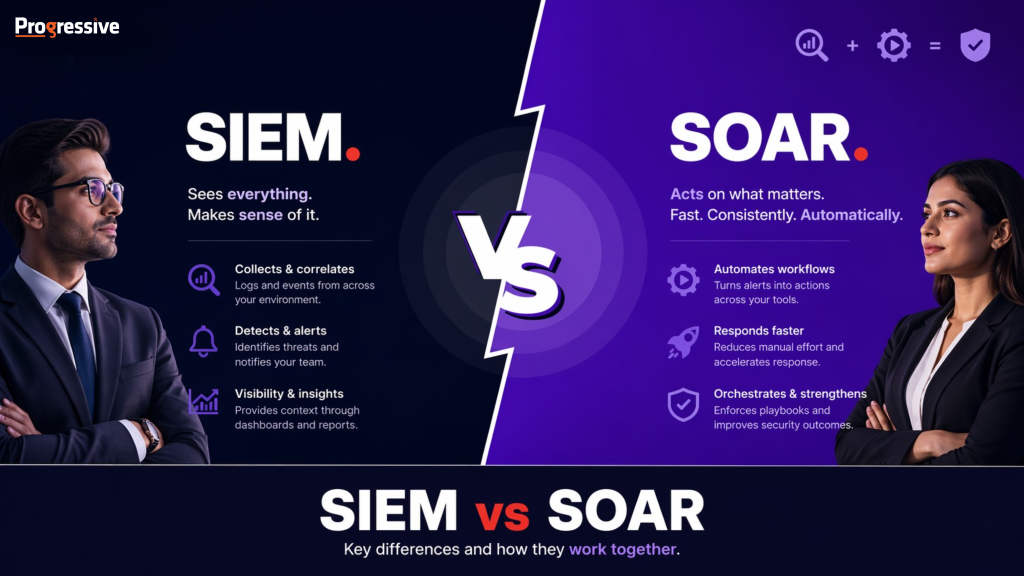
- SIEM vs SOAR: Key Differences and How They Work TogetherSIEM and SOAR are two of the most frequently referenced tools in enterprise security, and they often appear side by… Read more: SIEM vs SOAR: Key Differences and How They Work Together
- SOC — Security Operations Center ExplainedCyber threats don’t wait and neither should your defenses. Today’s attacks are faster, more targeted, and often go unnoticed until… Read more: SOC — Security Operations Center Explained
- DPDP Act Penalties: Understanding the Cost of Non-ComplianceThe DPDP Act backs its obligations with substantial financial penalties. These are not token fines — they are designed to… Read more: DPDP Act Penalties: Understanding the Cost of Non-Compliance
- Data Privacy Compliance in India: From Obligation to Competitive AdvantageIndia’s digital economy is growing at an unprecedented pace. With over 950 million internet users, rapid 5G adoption, and the… Read more: Data Privacy Compliance in India: From Obligation to Competitive Advantage
- DPDP Act vs GDPR: A Comparative Analysis for Global BusinessesIndia’s DPDP Act and the European Union’s GDPR share a common objective: protecting individuals’ personal data rights. Both establish consent-based… Read more: DPDP Act vs GDPR: A Comparative Analysis for Global Businesses
- Significant Data Fiduciaries Under the DPDP Act: Heightened Duties, Greater AccountabilityThe Central Government has the authority to classify any Data Fiduciary or class of Data Fiduciaries as Significant Data Fiduciaries… Read more: Significant Data Fiduciaries Under the DPDP Act: Heightened Duties, Greater Accountability
- Data Breach Notification Under the DPDP Act: The 72-Hour ImperativeIndia’s DPDP Act introduces mandatory data breach notification for the first time in Indian law. Prior to this legislation, there… Read more: Data Breach Notification Under the DPDP Act: The 72-Hour Imperative
- What is a Data Fiduciary? Everything You Need to KnowAs businesses continue to go digital, the amount of personal data being collected is growing rapidly. From websites to mobile… Read more: What is a Data Fiduciary? Everything You Need to Know
- Consent Management Under the DPDP Act: Building a Compliant FrameworkThe DPDP Act places consent at the centre of its regulatory architecture. Unlike some jurisdictions that offer multiple legal bases… Read more: Consent Management Under the DPDP Act: Building a Compliant Framework
- Data Principal Rights Under the DPDP Act: What Individuals Can DemandThe DPDP Act empowers Indian citizens with a set of enforceable rights over their personal data. These rights shift the… Read more: Data Principal Rights Under the DPDP Act: What Individuals Can Demand
- Data Protection in India: How the DPDP Act Transforms the Privacy LandscapeIndia’s data protection journey has been long and complex. For years, the Information Technology Act, 2000, and its 2011 rules… Read more: Data Protection in India: How the DPDP Act Transforms the Privacy Landscape
- DPDP Rules 2025 Explained: What Every Data Fiduciary Needs to KnowData protection in India has entered a decisive new chapter. After years of legislative deliberation and public consultation, the Ministry… Read more: DPDP Rules 2025 Explained: What Every Data Fiduciary Needs to Know
- DPDP Act Compliance: A Practical Roadmap for Indian Businesses in 2026The Digital Personal Data Protection Act, 2023 is now in force, with the DPDP Rules 2025 notified on November 13,… Read more: DPDP Act Compliance: A Practical Roadmap for Indian Businesses in 2026
- What is the DPDP Act? A 2026 Guide for BusinessesIf you’ve recently come across the term DPDP Act and are wondering what it means, you’re not alone. With India… Read more: What is the DPDP Act? A 2026 Guide for Businesses
- AI-Powered Managed IT Services: From Reactive Support to Proactive PartnershipThe managed IT services industry is at an inflection point. Businesses today don’t just want IT support, they want strategic… Read more: AI-Powered Managed IT Services: From Reactive Support to Proactive Partnership
- When the World Goes to War, Cyber Criminals Go to WorkOn February 28, 2026, coordinated military strikes in the Middle East triggered immediate cyber retaliation from Iran linked threat actors… Read more: When the World Goes to War, Cyber Criminals Go to Work
- Human + AI: The New Managed Services Workforce ModelLet me start with a confession. When I first heard the phrase “AI will replace managed services jobs,” my instinct was… Read more: Human + AI: The New Managed Services Workforce Model
- From Reactive to Predictive: AIOps in Modern IT Infrastructure ManagementIn today’s hyper-connected business environment, IT infrastructure is no longer just a support function-it is the backbone of digital transformation.… Read more: From Reactive to Predictive: AIOps in Modern IT Infrastructure Management
- DPDP Is Here. Is Your Data Architecture Ready?India’s Digital Personal Data Protection Act, 2023 (DPDP Act) has moved data protection from policy documents to system design. For… Read more: DPDP Is Here. Is Your Data Architecture Ready?
- Your Service Desk Is Bleeding Value. Fix It Now.For most enterprises, the IT service desk has become a silent value leak. Costs continue to rise. Ticket volumes remain… Read more: Your Service Desk Is Bleeding Value. Fix It Now.
- India’s GCC Moment: From Cost Arbitrage to Global Value CreationFor more than two decades, Global Capability Centers (GCCs) in India were largely seen through a single lens cost arbitrage.… Read more: India’s GCC Moment: From Cost Arbitrage to Global Value Creation
- Cybersecurity in the Age of AIAI has permanently changed the economics, velocity, and impact of cyber risk. For enterprises, cybersecurity is no longer a technical… Read more: Cybersecurity in the Age of AI
- Cybersecurity in 2026: From Protection to ResilienceFor years, cybersecurity strategies have been anchored in a single ambition: prevent the breach. That ambition, while necessary, is no… Read more: Cybersecurity in 2026: From Protection to Resilience
- Vulnerability Assessment vs Penetration Testing: What Your Company NeedsIn today’s digital-first world, cybersecurity is no longer optional—it is a business necessity. Organizations rely heavily on applications, cloud platforms,… Read more: Vulnerability Assessment vs Penetration Testing: What Your Company Needs
- Network Security Strategy for 2026: A Practical GuideAs digital transformation accelerates across industries, network security has emerged as a critical pillar of enterprise strategy. Organizations are increasingly… Read more: Network Security Strategy for 2026: A Practical Guide
- The Hidden ROI of Managed IT Services: Beyond Cost SavingsWhen organizations think about Managed IT Services, the conversation often begins and ends with cost savings. Outsourcing IT management is… Read more: The Hidden ROI of Managed IT Services: Beyond Cost Savings
- The Role of AI and Automation in Transforming Global Service Desks in 2025The year 2025 marks a decisive turning point for enterprise IT operations. With hybrid work now firmly established, and business… Read more: The Role of AI and Automation in Transforming Global Service Desks in 2025
- AI vs. AI: The Cybersecurity Arms Race Reshaping Digital DefenseIntroduction: When Machines Battle Machines Not long ago, cyberattacks were human vs. human — a hacker on one side, a… Read more: AI vs. AI: The Cybersecurity Arms Race Reshaping Digital Defense
- Future Trends: How Outsourcing Optimizes CAPEX and OPEX in IT Infrastructure ManagementIn today’s digital economy, enterprise IT infrastructure decisions are no longer purely technical—they are strategic financial choices. As organizations scale,… Read more: Future Trends: How Outsourcing Optimizes CAPEX and OPEX in IT Infrastructure Management
- Why Agentic AI Is Important for CybersecurityWhat happens when attackers move at machine speed, but defenders are still responding at human speed? This is the uncomfortable… Read more: Why Agentic AI Is Important for Cybersecurity
- AIOps: Transforming the Future of IT Infrastructure Management in IndiaOverview Enterprises across India are rapidly adopting digital technologies, cloud platforms, and hybrid IT environments. With this transformation comes complexity… Read more: AIOps: Transforming the Future of IT Infrastructure Management in India
- SIEM Sizing Calculator – The Next Evolution in Cyber DefenseModern businesses generate an enormous volume of security event logs every single day — from cloud apps, networks, servers, and… Read more: SIEM Sizing Calculator – The Next Evolution in Cyber Defense
- Cybersecurity Threat Hunting: A Complete Guide for Enterprise Security LeadersWhat is threat hunting? Cybersecurity Threat hunting is a proactive cybersecurity practice in which analysts continuously search through network, cloud,… Read more: Cybersecurity Threat Hunting: A Complete Guide for Enterprise Security Leaders
- Future-Ready Workplace Management Suite: The Next Big Leap in Employee ExperienceThe workplace is no longer a place. It’s an experience.In an era of hybrid work, global teams, and digital-first operations,… Read more: Future-Ready Workplace Management Suite: The Next Big Leap in Employee Experience
- Remote Infrastructure Management Services (RIMS): Driving Efficiency and Reliability in IT OperationsOverview Organizations are increasingly adopting Remote Infrastructure Management due to the growing complexity of hybrid and multi-cloud environments, the need… Read more: Remote Infrastructure Management Services (RIMS): Driving Efficiency and Reliability in IT Operations
- Vulnerability Assessment and Penetration Testing: Choosing the Right Cybersecurity ApproachVulnerability Assessment and Penetration Testing (VAPT) is a comprehensive security testing approach that combines automated scanning (vulnerability assessment) with simulated… Read more: Vulnerability Assessment and Penetration Testing: Choosing the Right Cybersecurity Approach
- Ransomware Defence for Banks: Key Strategies to Prevent, Detect & RespondIn recent years, banks have found themselves squarely in the crosshairs of ransomware gangs. What began as opportunistic attacks on… Read more: Ransomware Defence for Banks: Key Strategies to Prevent, Detect & Respond
- Building a Sustainable IT Ecosystem: Why Managed Services Are the Game ChangerThe IT paradox: Every server we power, every device we deploy, and every workload we migrate brings us closer to… Read more: Building a Sustainable IT Ecosystem: Why Managed Services Are the Game Changer
- Email Phishing: What It Is, Why It Matters, and How to Build Organizational ResilienceLet’s start with a scenario It’s Monday morning. You’re catching up on emails over a cup of coffee. One message… Read more: Email Phishing: What It Is, Why It Matters, and How to Build Organizational Resilience
- Why Is Application Management Crucial for Your Business’s Operational Resilience?The Hidden Risks Lurking Beyond Your Applications Most organizations prioritize maintaining their servers and networks—but overlook the critical operational gaps… Read more: Why Is Application Management Crucial for Your Business’s Operational Resilience?
- Why Is Dark Web Monitoring Crucial for Your Business’s Security?In the vast, interconnected world of the internet, businesses often focus on protecting their visible assets: websites, servers, and internal… Read more: Why Is Dark Web Monitoring Crucial for Your Business’s Security?
- The VAPT Evolution: From Traditional VAPT to a Structured, Managed VAPT SolutionIntroduction Vulnerability Assessment and Penetration Testing (VAPT) has become more than a technical formality — it’s now a critical part… Read more: The VAPT Evolution: From Traditional VAPT to a Structured, Managed VAPT Solution
- How Cybersecurity Is Becoming a Critical Priority in Engineering & Infrastructure ProjectsDid you know a single cyberattack on an infrastructure project can halt operations, delay timelines, inflate costs, and compromise national… Read more: How Cybersecurity Is Becoming a Critical Priority in Engineering & Infrastructure Projects
- The New Rules of Cyber Defense: Why Organizations Are Shifting to 24×7 Intelligent SecurityCyber attackers have evolved their strategies in 2025, demanding organizations to rethink their cyber security, encryption practices, and risk management… Read more: The New Rules of Cyber Defense: Why Organizations Are Shifting to 24×7 Intelligent Security
- Future Ready: Enabling Digital Transformation Through Intelligent CybersecurityIn a world that’s always online, always connected, and rapidly evolving, one thing is certain—your business’s success depends on its… Read more: Future Ready: Enabling Digital Transformation Through Intelligent Cybersecurity
- AIOps: The Future of IT Service ManagementWhat if your IT service management could predict problems before they happen? What if it could solve issues on its… Read more: AIOps: The Future of IT Service Management
- Generative AI in Business: Driving Innovation and Transforming OperationsAs technology continues to break new ground at an unprecedented pace, businesses are facing a defining moment—where they must adapt… Read more: Generative AI in Business: Driving Innovation and Transforming Operations
- The Scope of Pharmaceutical Cybersecurity in 2025Pharmaceutical companies are prime targets for cyberattacks, with their extensive supply chains, valuable intellectual property, and sensitive personal data offering… Read more: The Scope of Pharmaceutical Cybersecurity in 2025
- From Reactive to Proactive: Revolutionize Your Cybersecurity with AI-Powered IT/OT SecOpsCyber threats aren’t waiting for you to respond. They evolve, adapt, and strike—often when you least expect them. So why… Read more: From Reactive to Proactive: Revolutionize Your Cybersecurity with AI-Powered IT/OT SecOps
- How IT/OT Security Assessments Can Protect Your Business in 2025 and BeyondThe digital age has transformed the way businesses operate—embracing new technologies, expanding global reach, and tapping into data-driven insights. But… Read more: How IT/OT Security Assessments Can Protect Your Business in 2025 and Beyond
- 2025 Global Service Desk Trends: What to Expect and Prepare ForThe global service desk landscape is evolving at a rapid pace, driven by emerging technologies, shifting business models, and growing… Read more: 2025 Global Service Desk Trends: What to Expect and Prepare For
- Revolutionizing Business: Why Managed IT Services are Key to Successful Digital TransformationToday, technology is no longer just a tool for efficiency; it’s the engine powering innovation and growth across industries. As… Read more: Revolutionizing Business: Why Managed IT Services are Key to Successful Digital Transformation
- Digitization, Digitalization, and Digital Transformation: Key Drivers in the IT Managed Services EraThe rapid pace of technological change has brought about a pivotal moment for businesses. Organizations are finding themselves at the… Read more: Digitization, Digitalization, and Digital Transformation: Key Drivers in the IT Managed Services Era
- Outsourcing IT Managed Services vs. In-House IT Operations: Which Strategy Drives Business Success?In a world where business success increasingly relies on efficient technology, companies are left with a critical question: Should IT… Read more: Outsourcing IT Managed Services vs. In-House IT Operations: Which Strategy Drives Business Success?
- Threat Hunting: A Proactive Approach to CybersecurityIn today’s rapidly evolving cyber landscape, traditional defenses are no longer sufficient to protect organizations from sophisticated threats. Attackers are… Read more: Threat Hunting: A Proactive Approach to Cybersecurity
- The Role of IT Managed Services in Meeting ESG (Environmental, Social, and Governance) GoalsIn an era where sustainability, social responsibility, and ethical governance are not just buzzwords but imperatives, businesses are increasingly aligning… Read more: The Role of IT Managed Services in Meeting ESG (Environmental, Social, and Governance) Goals
- Protect Your Endpoints, Secure Your Future: The Vital Role of Endpoint Security in Business ContinuityImagine navigating your business through the digital landscape when suddenly — BAM! — you’re hit by a cyber onslaught. Malware… Read more: Protect Your Endpoints, Secure Your Future: The Vital Role of Endpoint Security in Business Continuity
- Unified Cybersecurity: The Power of SOAR, SIEM, VAPT, and Zero Trust TogetherWhen you hear “cybersecurity,” it’s easy to think of it as a singular defense against threats. But the reality is,… Read more: Unified Cybersecurity: The Power of SOAR, SIEM, VAPT, and Zero Trust Together
- Navigating Good vs Bad AI: Insights for IT Managed ServicesArtificial Intelligence (AI) has swiftly emerged as a pivotal force in technological innovation, transforming numerous industries. While the potential benefits… Read more: Navigating Good vs Bad AI: Insights for IT Managed Services
- Transforming Business Operations with IT Managed Services: The Key to Digital ExcellenceEver wondered what truly fuels seamless and efficient digital operations in the dynamic business environment of today? The answer lies… Read more: Transforming Business Operations with IT Managed Services: The Key to Digital Excellence
- Detect, Analyze, respond: The Ultimate Guide to Managing Network AnomaliesIn the rapidly evolving digital world, where downtime can equate to lost revenue and compromised security, keeping your network running… Read more: Detect, Analyze, respond: The Ultimate Guide to Managing Network Anomalies
- The Role of IT Managed Services in Digital Transformation: A Roadmap for BusinessesIn the rapidly evolving digital age, businesses must stay ahead by adopting advanced technologies and optimizing their operations. Digital transformation,… Read more: The Role of IT Managed Services in Digital Transformation: A Roadmap for Businesses
- How to Leverage IT Asset Management for Enhanced CybersecurityIn the contemporary digital era, the intersection of IT Asset Management (ITAM) and cybersecurity has gained critical importance. Effective ITAM… Read more: How to Leverage IT Asset Management for Enhanced Cybersecurity
- What is SIEM and Its Contribution to SOC Operations?In today’s digital era, organizations face an unprecedented number of cyber threats. To manage and mitigate these threats effectively, Security… Read more: What is SIEM and Its Contribution to SOC Operations?
- The Importance of 24×7 NOC Support on Business OperationsIn an increasingly connected and digitally dependent world, the role of a Network Operations Center (NOC) cannot be overstated. For… Read more: The Importance of 24×7 NOC Support on Business Operations
- The Impact of AI on the Cyber Threat Landscape: The State of AI in Cybersecurity in 2024As we step into the ever-evolving landscape of cybersecurity, the intersection of artificial intelligence (AI) and digital threats takes center… Read more: The Impact of AI on the Cyber Threat Landscape: The State of AI in Cybersecurity in 2024
- The Rise of AI: How Artificial Intelligence is Revolutionizing Global Service Desk OperationsIn the dynamic world of modern business, one thing is clear: Artificial Intelligence (AI) is a game-changer. It’s like the… Read more: The Rise of AI: How Artificial Intelligence is Revolutionizing Global Service Desk Operations
- The Future of Digital Infrastructure ServicesIn the digital age, businesses heavily rely on technology for their operations, emphasizing the critical importance of digital infrastructure services.… Read more: The Future of Digital Infrastructure Services
- A Definitive Guide to Security HardeningSecurity hardening is a proactive cybersecurity approach aimed at fortifying the defenses of systems, networks, and applications. It involves identifying… Read more: A Definitive Guide to Security Hardening
- An In-Depth Guide to Database ManagementIn today’s business landscape, effective data management is paramount for organizational success. A Database Management System (DBMS) serves as the… Read more: An In-Depth Guide to Database Management
- Unlocking Efficiency and Connectivity: The Power of Global Service Desk and OutsourcingIn today’s interconnected world, businesses operate across borders, time zones, and cultures. With this expansion comes the need for robust… Read more: Unlocking Efficiency and Connectivity: The Power of Global Service Desk and Outsourcing
- Mastering Cybersecurity: A Comprehensive Guide to VAPT and the Ripple Effect of Data BreachesWelcome to the realm of cybersecurity mastery! In this guide, we delve into the intricate world of Vulnerability Assessment and… Read more: Mastering Cybersecurity: A Comprehensive Guide to VAPT and the Ripple Effect of Data Breaches
- Unveiling Cybersecurity Excellence: A Comprehensive Guide of SIEM TechnologyIn today’s rapidly evolving digital landscape, businesses face an ever-growing threat landscape from cybercriminals. As organizations increasingly rely on digital… Read more: Unveiling Cybersecurity Excellence: A Comprehensive Guide of SIEM Technology
- Why Do We Need Managed Security Operations Center (SOC) Providers: A Comprehensive OverviewIn an era dominated by digital advancements, businesses face a growing array of cyber threats that evolve at an unprecedented… Read more: Why Do We Need Managed Security Operations Center (SOC) Providers: A Comprehensive Overview
- What is NOC and How Network Operations Centers (NOCs) Work?In the vast and interconnected world of technology, the smooth functioning of networks is crucial. Behind the scenes, ensuring the… Read more: What is NOC and How Network Operations Centers (NOCs) Work?
- Unlocking the Power of Zero Trust Security: A Comprehensive Guide to Implementation ExcellenceIn an era dominated by sophisticated cyber threats and continuously evolving attack vectors, the inadequacies of traditional security models have… Read more: Unlocking the Power of Zero Trust Security: A Comprehensive Guide to Implementation Excellence
- Revolutionizing Digital Transformation: How the Amazing Fractional CIO Impacts Industry 4.0In the ever-evolving world of business and technology, the term “Industry 4.0” has gained significant attention. It represents the latest… Read more: Revolutionizing Digital Transformation: How the Amazing Fractional CIO Impacts Industry 4.0
- 9 Reasons: Why Does Business Needs a Complete Digital Workplace PlatformIn an era where remote work, digital collaboration, and seamless productivity are paramount, organizations must adapt to thrive. Enter the… Read more: 9 Reasons: Why Does Business Needs a Complete Digital Workplace Platform
- The Impact of Neglecting IT Asset Management on Your OrganizationIn the fast-paced world of technology, where innovation and digital transformation are paramount, organizations are constantly upgrading their IT infrastructure.… Read more: The Impact of Neglecting IT Asset Management on Your Organization